Twelfth Grade, Cybersecurity Science Projects (4 results)
Personal messages, photos, banking information, credit card numbers, names, addresses, health records—a lot of
your family's private information is stored on computers and zipping through the Internet!
Cybersecurity is the act of keeping information, ranging from embarrassing baby photos to national secrets, private and viewed by only the right people.

|
Select a resource
Sort by
|
We use passwords every day for our email and other computer accounts. How secure is the password that you use? How hard would it be for someone to guess your password? How hard is it to write a computer program to guess a password? You can see for yourself by writing a simple password guesser in the computer language Python. We will get you started with some ideas, a little sample code, and a few passwords for your computer program to try and guess.
Read more
Featured
Have you heard that garlic powder is supposed to inhibit the growth of bacteria? Which do you think would make a better disinfectant: a solution of garlic powder or a solution of bleach? This project shows you a straightforward way to compare the effectiveness of different disinfectants (or other antimicrobial agents), by measuring zones of inhibition on a culture plate.
Read more
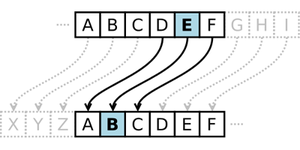
When you hear the word "encryption," you might think about modern computers and things like email and online bank accounts. But did you know that encryption has been around for thousands of years? In this project you will learn about the Caesar cipher, a simple type of encryption that replaces each letter of the alphabet with another letter, and demonstrate how a modern computer can crack this ancient code in just a few seconds.
Read more
New
Artificial intelligence (AI) programs can now generate photorealistic pictures of people who do not exist in the real world. How can you tell if a picture is of a real person or a fake, AI-generated person? What features of the picture do people use to decide whether the face is real or AI-generated? In this project, you will explore these questions as you ask volunteers to look at both real and AI-generated pictures of human faces.
Read more
You might think that one sure-fire way to keep your computer safe from hackers is to disconnect it from the internet entirely. But did you know that even without internet, a computer can transmit data using light, sound, vibrations, or even heat? In this project, you will investigate how a spy or hacker can steal data from an "air-gapped" computer that has no internet connection. You can even use a smartphone equipped with a sensor app to demonstrate how the data can be picked up by a nearby…
Read more
How many websites do you have accounts with that store personal information like your name, email, phone number, or mailing address? If the people running these websites are not careful, hackers could gain unauthorized access to, and even change or delete, your information. They can do this using something called SQL injection, which involves entering malicious code into text fields on a website. In this project you will learn how SQL injection works and figure out how to prevent it.
Read more
|
Explore Our Science Videos
Dancing Robot
Balloon Car: 2015 Engineering Challenge
Marble Machine: 2016 Engineering Challenge